Introduction
In the rapidly evolving world of cybersecurity, the Android platform continues to be a prime target for malicious actors, with the resurgence of the Vultur banking trojan serving as a stark reminder of the persistent threats facing mobile devices. As businesses and individuals increasingly rely on their smartphones and tablets for a wide range of activities, the need for comprehensive security solutions has never been more pressing.
Francium Networks, a leading provider of managed security services, is committed to empowering organizations and individuals to proactively defend against these evolving mobile threats. In this comprehensive blog post, we will delve into the details of the Vultur banking trojan's recent upgrades, explore the potential consequences of this sophisticated malware, and showcase how Francium Networks' security solutions can help safeguard your mobile devices and sensitive data.
The Evolving Threat of the Vultur Android Banking Trojan
The Vultur Android banking trojan, first disclosed in early 2021, has resurfaced with a suite of new features and improved anti-analysis and detection evasion techniques, enabling its operators to remotely interact with infected mobile devices and harvest sensitive data.
Vultur's latest iterations have demonstrated a significant shift in focus towards maximizing remote control over compromised devices. The malware now boasts the ability to execute a wide range of commands, including clicks, scrolls, and swipes, through Android's accessibility services. Additionally, Vultur can download, upload, delete, install, and locate files, as well as prevent victims from interacting with predefined apps, display custom notifications, and even bypass lock screen security measures.
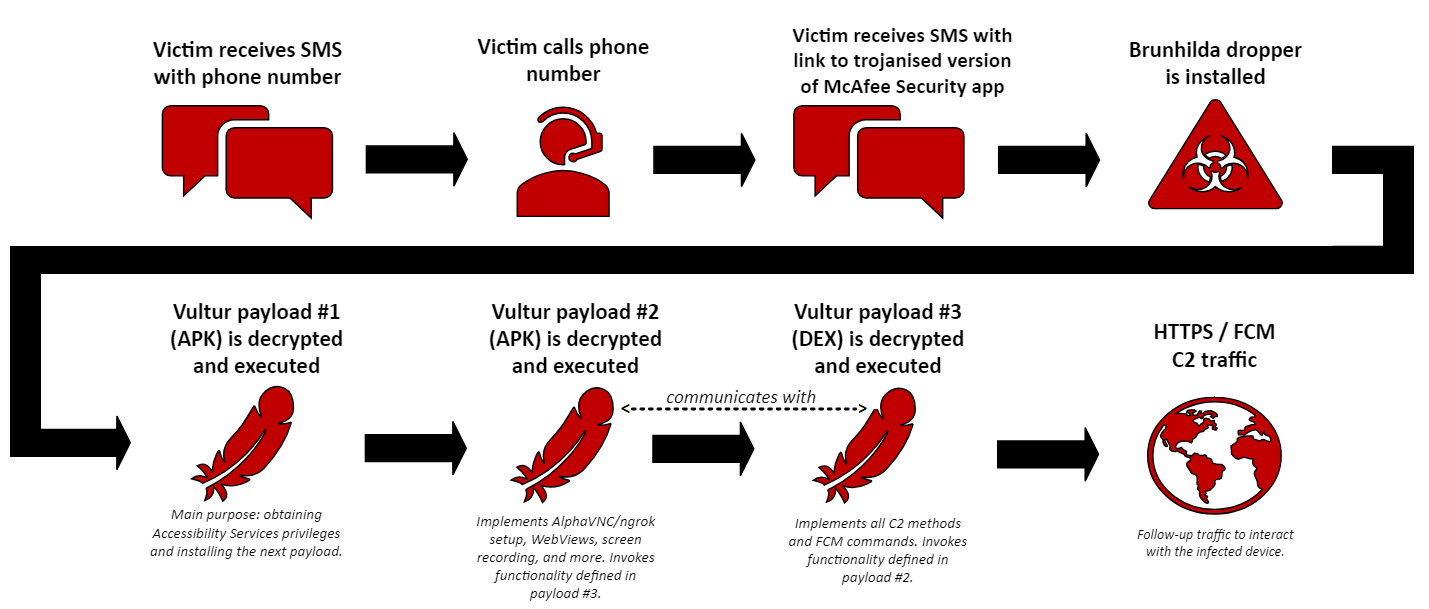
The threat actors behind Vultur have also employed sophisticated distribution tactics, leveraging trojanized dropper apps on the Google Play Store that masquerade as legitimate authenticator and productivity applications. These droppers are part of a broader dropper-as-a-service (DaaS) operation called Brunhilda, which also involves the use of telephone-oriented attack delivery (TOAD) techniques to lure victims into installing the malware.
The Vultur banking trojan's advanced remote control capabilities, coupled with its evasive distribution methods, make it a formidable threat to both individuals and organizations that rely on Android devices for their daily operations and access to sensitive data. As the malware continues to evolve, the need for robust security measures to protect against such sophisticated mobile threats becomes increasingly crucial.
Defending Against the Vultur Threat with Francium Networks
To effectively safeguard your mobile devices and the data they contain against the Vultur banking trojan and other emerging mobile threats, Francium Networks offers a comprehensive suite of security solutions designed to provide robust protection and peace of mind.
- Mobile Threat Detection and Response:
Francium Networks' advanced threat detection algorithms and incident response capabilities are tailored to identify and mitigate the signature of the Vultur trojan and other sophisticated mobile malware, ensuring that your devices are continuously monitored and swiftly protected against active threats. - Secure Mobile Device Management:
Our comprehensive mobile device management (MDM) solutions allow you to centrally manage and enforce security policies across your organization's Android and iOS devices, ensuring that they are configured with the appropriate security controls and access restrictions to mitigate the risks of mobile threats. - Vulnerability and Patch Management:
Francium Networks' team of cybersecurity experts closely monitors the evolving landscape of mobile vulnerabilities, proactively identifying and addressing potential weaknesses in your device operating systems and applications to prevent exploitation by threats like the Vultur trojan. - User Awareness and Security Training:
Recognizing that the human element is a critical component of mobile security, Francium Networks offers comprehensive security awareness training programs to educate your employees on the latest mobile threat vectors, phishing tactics, and the importance of maintaining vigilance to protect against malicious applications and activities. - Incident Response and Digital Forensics:
In the event of a successful mobile device compromise, our incident response team is equipped to swiftly contain the threat, conduct thorough forensic investigations, and guide you through the recovery and remediation process, minimizing the impact and ensuring the integrity of your data.
Conclusion
The resurgence of the Vultur Android banking trojan, with its enhanced remote control capabilities and evasive distribution tactics, serves as a stark reminder of the persistent and evolving threats facing mobile devices in the modern digital landscape. As businesses and individuals increasingly rely on their smartphones and tablets for a wide range of activities, the need for comprehensive security solutions has become paramount.
By partnering with Francium Networks, organizations and individuals can leverage our expertise in mobile security, threat detection, and incident response to effectively mitigate the risks posed by the Vultur trojan and other sophisticated mobile malware. Our holistic security approach, which combines advanced technologies, security best practices, and user education, can help you safeguard your mobile devices and the sensitive data they contain, ensuring your continued productivity and peace of mind in the face of these emerging threats.
Don't let the Vultur banking trojan or other mobile threats compromise your security and privacy. Invest in a proactive and comprehensive mobile security strategy with Francium Networks and stay ahead of the curve in the ever-evolving world of cybersecurity.




